Table Of Contents

Have I Been Pwned vs Detectico: Best Have I Been Pwned Alternative
Skilled techies mastering location data.
In an era where data breaches are increasingly common, tools like “Have I Been Pwned” have become crucial for digital security. Statistics show that in 2023 alone, over 72% of businesses globally experienced ransomware attacks, marking a significant increase over the preceding five years and representing the highest reported figure to date.
It’s important to recognize that it’s not just businesses that suffer. Ordinary people are also affected, so services like Have I Been Pwned play a pivotal role in identifying and mitigating data breaches. This article will delve into the features and effectiveness of Have I Been Pwned, introduce its best alternatives like Detectico, LeakCheck, and Scannero, and compare its capabilities in handling email leaks.
What is “Have I Been Pwned?”
It is a widely recognized online platform designed to help internet users discover if their data has been compromised in a data breach. You would use it if you ever wondered “Is my email compromised”. “Pwned” originates from video game culture, where it’s a leetspeak version of “owned,” stemming from the proximity of the “o” and “p” keys on a keyboard.
The term is commonly used to indicate that someone or something has been overtaken or compromised. So, “pwned” transitioned from hacker slang to becoming the internet’s preferred taunt.
By aggregating data from various sources made public after breaches, Have I Been Pwned offers a comprehensive search database. Users can enter their email addresses to see if they appear in any recorded data breaches, thereby providing an early warning system to take necessary security measures.
How Does Have I Been Pwned Work?
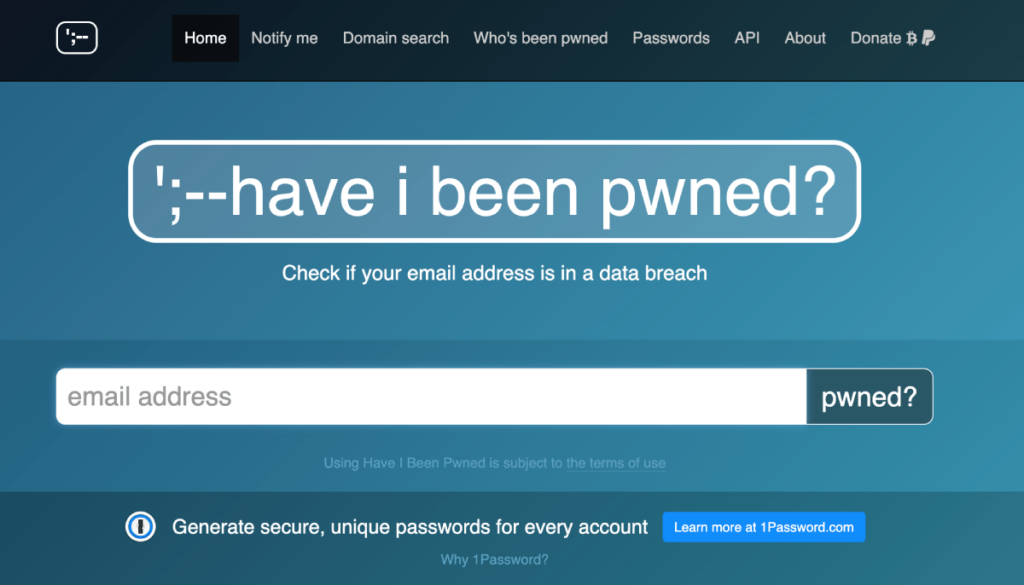
Well, Have I Been Pwned is a website that can help those worried that their personal information might have been exposed in a data breach It collects information from public data breaches and stores them in a searchable database. Have I Been Pwned uses k-anonymity to protect your privacy when searching. This means that your sensitive search information is converted into a hash, so it’s never stored or transmitted.
Key Features of Have I Been Pwned
- Email Leak Detection: Scans databases for leaked email addresses;
- Data Breach Notifications: Alerts users about new breaches;
- Security Measures: Offers suggestions for improving digital safety.
Who Needs to Use Have I Been Pwned?
- Individual users to protect personal information;
- Businesses for safeguarding customer and employee data;
- Security Professionals: As a tool for risk assessment;
- Anybody who wants to check was their email compromised.
Introducing The Best Have I Been Pwned Alternative
In the next paragraph, we’ll unveil an excellent “Have I been Pwned” alternative offering users insights into every compromised email address. The choices we’ve made are user-friendly and ensure your online safety without the technical fuss.
What is Detectico?
Detectico is an app that tackles various privacy concerns. This versatile platform:
- tracks a call’s origin, gives you insights into location, ownership, and potential risks associated with the number;
- shields your email privacy, checking if your data is exposed to hackers, with its email hack checker.
Detectico ensures a safer online experience, merging cutting-edge solutions with a user-friendly design. Explore Detectico – your go-to defense in the dynamic digital landscape.
Detectico’s Approach to Email Leak Check
Detectico revolutionizes email security with its innovative approach to doing a quick check if your email has been hacked. It enhances email security by swiftly and efficiently checking for potential compromises. Detectico prioritizes email security through a meticulous approach, utilizing secure sources and robust methodologies to ensure a proactive stance against any email breach.
Have I Been Pwned vs Detectico Email Leak Check Features Comparison
User Experience
To offer precise insights into the user experience of two reviewed apps, we present Trustpilot and Sitejabber ratings, two of the most popular websites dedicated to providing reviews, alongside real user reviews for each service:
- Detectico has 3.4 stars on Trustpilot and 4.5 stars on Sitejabber. Users noted great outcomes and stated that it performed exactly as expected. However, a few mentioned issues when they didn’t unsubscribe, resulting in charges for unnecessary check if email is compromised;
- “Have I been Pwned” has 2.5 stars on Trustpilot and doesn’t have any ratings on Sitejabber. Honestly, no reviews for a website with such high traffic raise suspicions. Also, users expressed difficulty in canceling subscriptions and reported disappointment in entering their email accounts, confirming their accounts were secure, only to receive spam emails later.
The varied user experiences highlight the importance of considering both positive and negative aspects when choosing an email security service.
User Interface Comparison
A user-friendly interface can significantly impact the overall experience. When comparing these two services:
- Detectico Email Leak Check takes a modern and sleek approach, providing users with a visually appealing interface. The platform prioritizes simplicity without compromising on functionality, offering a seamless email breach check;
- Have I Been Pwned boasts a straightforward and intuitive design. Users can easily navigate through the site to check the security status of their email addresses, with a minimalistic approach that focuses on efficiency.
Thus, platforms cater to varying preferences, with Have I Been Pwned’s simplicity contrasting Detectico’s visually engaging design.
Email Leak Check Effectiveness and Accuracy
The service’s accuracy guarantees that individuals receive reliable information, leading to the following comparison:
- Detectico’s advanced algorithms can determine if your private data is vulnerable to potential hackers, providing accurate insights, and empowering users to navigate the complexities of digital security effortlessly.
- Pwned email checking website also delivers precise and reliable insights.
In conclusion, both Detectico and Have I Been Pwned stand out for their commitment to accuracy and reliability in providing insights into email leak checks.
List of 3 Best Have I Been Pwned Alternatives
With the commitment to user privacy in detecting potential threats, we’ve gathered three of the best sites like “Have I Been Pwned”.
- Detectico
Detectico provides users with a comprehensive and user-friendly platform to check any email data breach and adds an extra layer of privacy by employing anonymizing technology. Users can receive real-time alerts if their email addresses are associated with any breaches, empowering them to take immediate action to secure their accounts.
- LeakCheck
LeakCheck is another comprehensive tool offering detailed reports on data breaches. This helps in mitigating potential risks associated with digital data exposure.
- Scannero
Scannero focuses on real-time alerts and has a user-friendly interface. With Scannero, stay one step ahead in the ongoing battle against cyber threats, ensuring a safer and more secure online experience.
Which App Should You Choose?
Choosing the right app for safeguarding your digital identity involves exploring alternatives beyond Have I Been Pwned, ensuring a more comprehensive defense against the prevalent risks of data breaches, leaks, and exposure.
It depends on your preferences to choose the app that suits you best for protecting your digital identity. You’ll have a clear understanding of which tool is the best when you clarify your needs.
Conclusion
We hope we’ve managed to give a comprehensive review of “Have I been Pwned” as well as its alternatives. Try out solutions like Detectico, LeakCheck, and Scannero to reduce risks and keep your information safe, to stay safe online, it’s better to use different ways against cyber threats. Always stay alert and make secure choices to stay ahead of the tricky digital threats we face today!